End-to-End Encryption
All messages are encrypted using ECDH (Elliptic Curve Diffie-Hellman) key exchange. Messages can only be decrypted by the intended recipient. Relay nodes transport ciphertext they cannot read.
- ECDH key exchange for shared secret derivation
- Cryptographic message signing prevents tampering
- Relays are blind couriers ‐ they can't read content
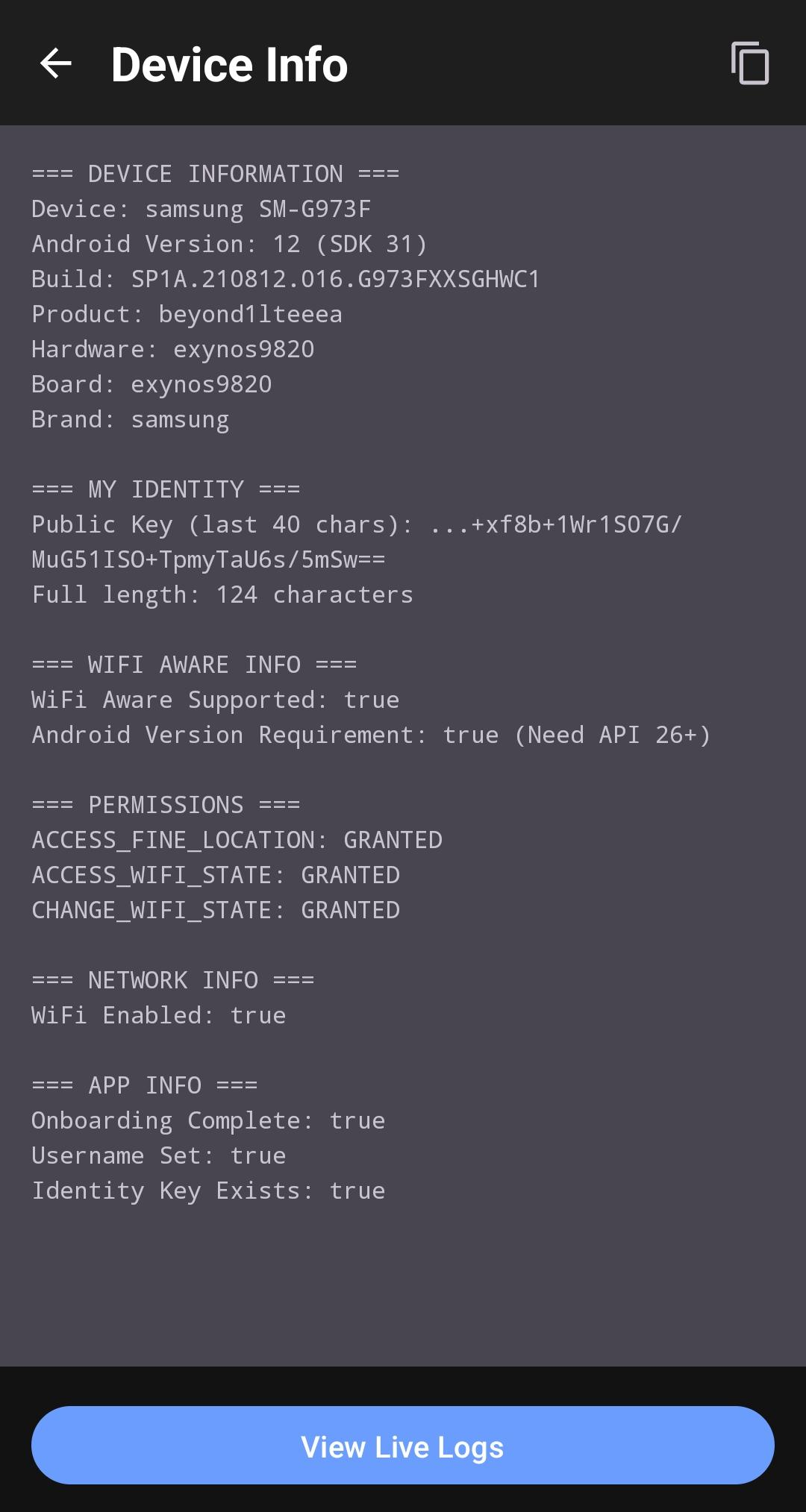
Hardware-Backed Key Storage
Your identity private keys are encrypted at rest using AES-256-GCM via the Android Keystore. The master key never leaves the secure hardware (TEE/StrongBox), protecting against root extraction and forensic analysis.
- AES-256-GCM encryption at rest
- Keys stored in TEE/StrongBox secure hardware
- Protection against root extraction
- Automatic migration from legacy storage
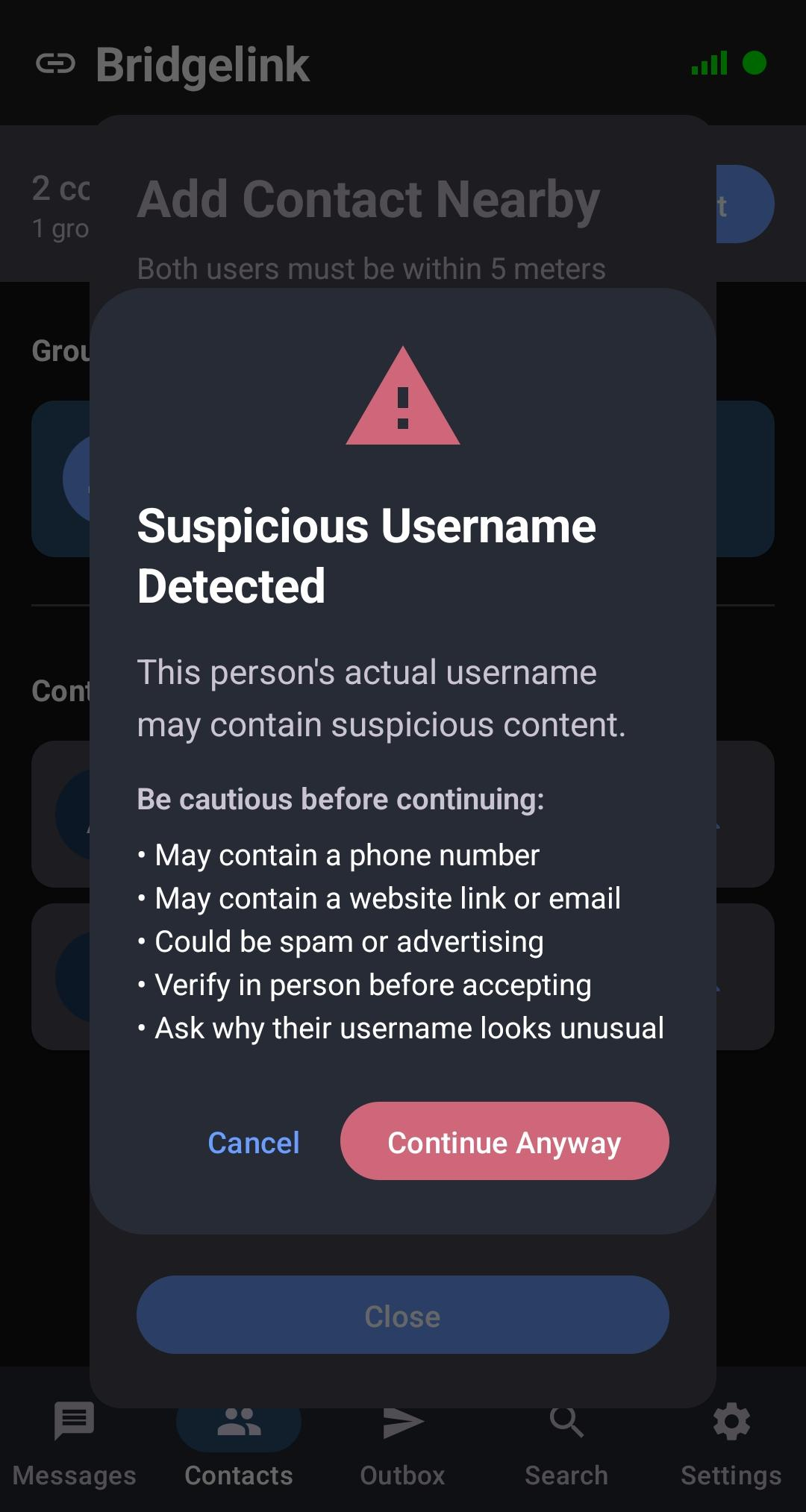
Anti-Billboard Protection
During pairing, users appear as random 3-word names generated from a 2048-word list (8.5 billion combinations). This prevents bad actors from broadcasting phone numbers or URLs as usernames.
- Random discoverable names (e.g., "apple-bridge-cloud")
- Chosen usernames hidden until PIN verification
- Suspicious pattern detection for phone numbers, URLs, and emails
- Color-coded warnings (green = safe, red = suspicious)
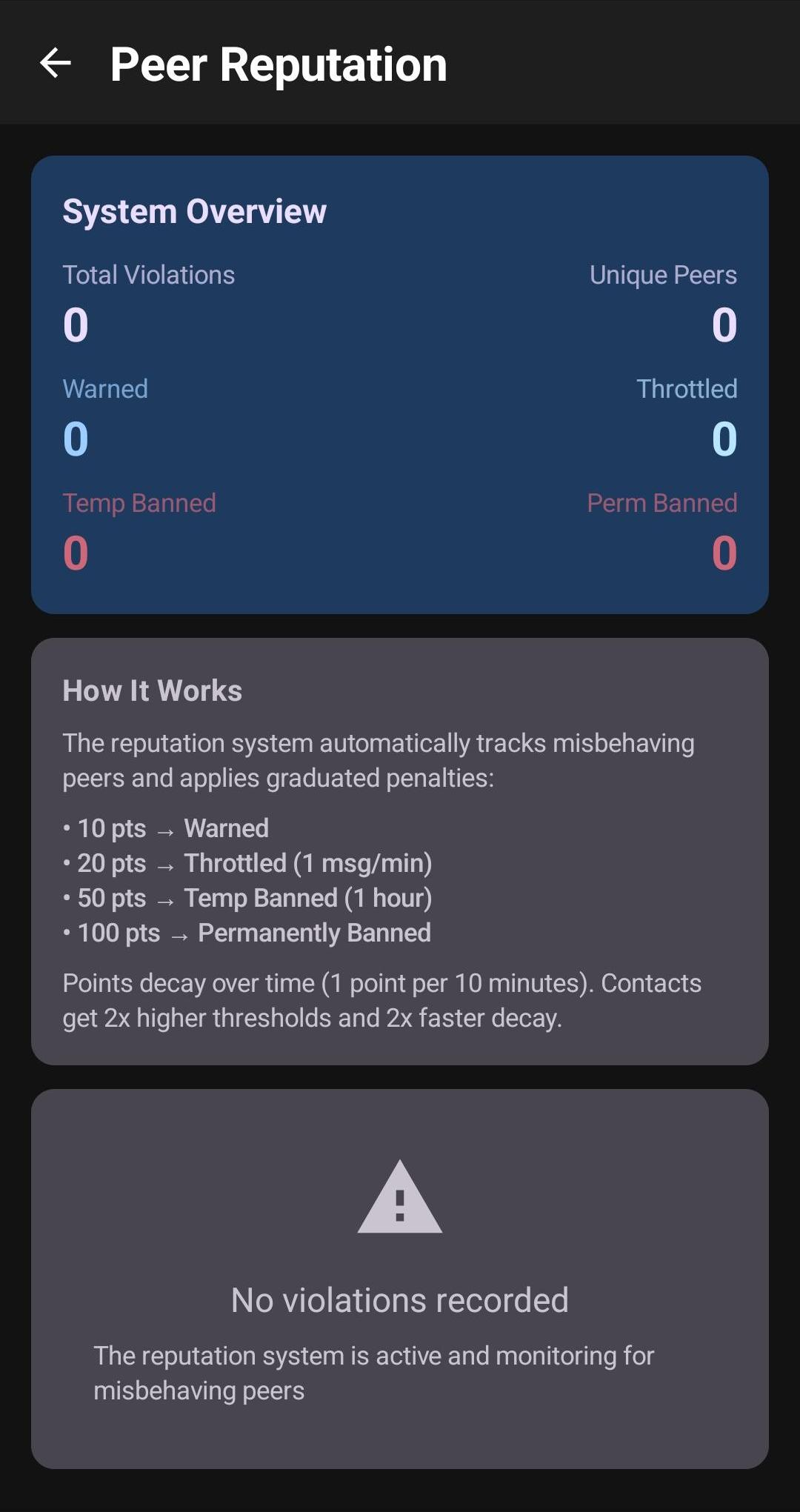
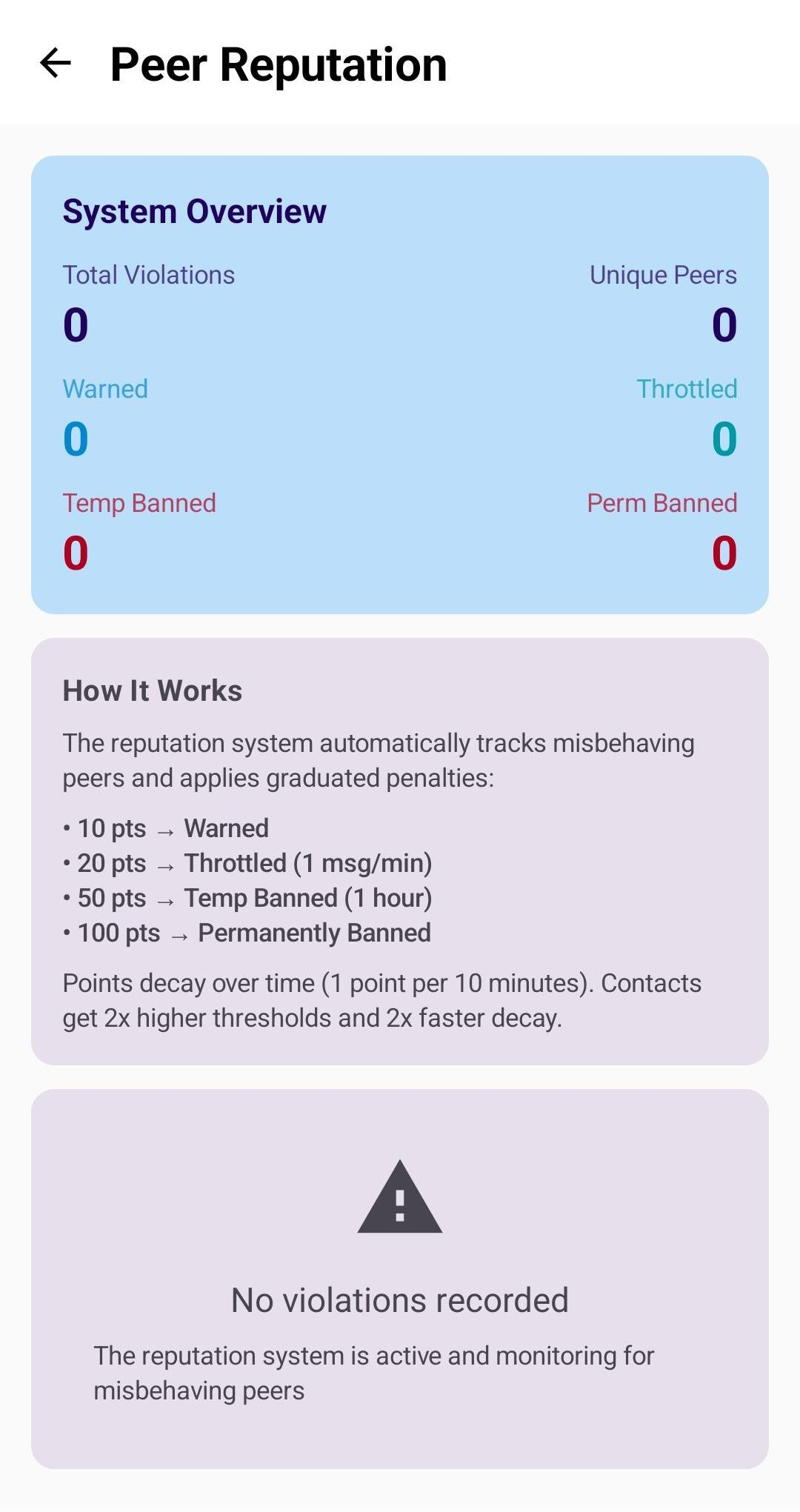
Peer Reputation System
An automatic graduated penalty system that detects and handles bad actors without user intervention. Points accumulate for protocol violations, with penalties escalating from warnings to permanent bans.
- Automatic decay: 1 point per 10 minutes (recovery from transient issues)
- Contact protection: 2x higher thresholds, 2x faster decay
- Silent penalties: No feedback to attackers
- 21 violation types covering all protocol aspects